DMARC
Though Cisco email security appliances (ESA) can be configured to send DMARC aggregate (RUA) reports, they have a limited number of daily DMARC reports they provide. This limit can be easily reached by organizations sending large volumes of email, especially if multiple subdomains are seen in the From header of messages received. The number of subdomains seen is an issue because of a deficiency in how the Cisco IronPort system generates DMARC reports. Instead of creating a single XML report containing data for the top-level domain and any subdomains (e.g. example.com along with www.example.com, server.example.com, etc), each server instance generates a completely separate report for each—this causes the limit to be reached rapidly. Increasing the daily limit will ensure that you have the proper visibility and are helping other organizations with their DMARC projects. The daily DMARC report default setting is 1000, which can be increased only through the command-line
Here’s some long-time-coming news from Microsoft, one of the world’s largest mailbox providers: they have started rolling out changes to honor DMARC policies as published in a domain’s DNS. Microsoft will now be treating the p=reject policy as intended; email failing DMARC authentication will not be delivered. Microsoft had been treating the DMARC policies of p=quarantine and p=reject the same way; email failing DMARC with a p=reject policy was delivered to the spam folder. Microsoft said they had operated this way “because some legitimate email may fail DMARC. For example, a message might fail DMARC if it’s sent to a mailing list that then relays the message to all list participants. If Microsoft 365 rejected these messages, people could lose legitimate email and have no way to retrieve it. Instead, these messages will still fail DMARC but they’ll be marked as spam and not rejected.” Microsoft signaled the change to
Updated July 17, 2023 to reflect new statistics from the SBA. dmarcian’s MSP Program Manager, Joe Garner, offers his thoughts on MSPs and their ever increasing role in protecting small and medium businesses from digital attacks. COVID shows the importance of MSPs as a vital touchpoint with the cybersecurity world There was a time in the not-too-distant past when most small businesses didn’t need any IT expertise beyond setting up printers and configuring accounting software, as most of their business was in real-time and in person. As COVID transformed the world, these businesses began adopting digital strategies for the first time to handle operations like digital commerce and remote workforces, and widespread digital transformation began. According to Salesforce’s 2021 “Small and Business Trends” report, 71% of growing small- and medium- sized businesses (SMBs) survived the pandemic by going digital, and 66% say their businesses could not have survived the pandemic
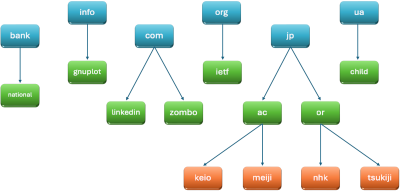
We often get questions about how DMARC policies apply to subdomains and how to establish a subdomain policy. Here’s some information to provide clarity and answer those questions. Because subdomains contend with the same abuse potential as parent domains, aka top-level or root domains, the astute authors of the DMARC control wrote specific conditions for subdomain policies. It goes like this: subdomains inherit the parent domain’s DMARC policy unless you indicate a subdomain policy using the sp= tag in the parent DMARC record or publish a p= tag on a subdomain. Keeping in mind that cybercriminals leverage unprotected subdomains for phishing exploits, it’s important to have a DMARC deployment plan for every subdomain you create, whether the parent domain DMARC policy is inherited, an sp= tag is published to rule the subdomains, or a p= tag is indicated for the subdomain. The DMARC policy definitions and actions apply to subdomain
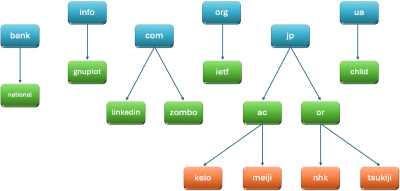
The Messaging, Malware, and Mobile Anti-Abuse Working Group, or M3AAWG, has released a blog post and white paper calling for the creation of an industry coalition to support the Public Suffix List (PSL). The PSL is an initiative under the Mozilla Foundation, and identifies the parts of the Internet domain name space under which organizations […]
The Messaging, Malware, and Mobile Anti-Abuse Working Group, or M3AAWG, has released a blog post and white paper calling for the creation of an industry coalition to support the Public Suffix List (PSL). The PSL is an initiative under the Mozilla Foundation, and identifies the parts of the Internet domain name space under which organizations […]
Investment Scams Costliest The FBI’s Internet Crime Complaint Center (IC3) has released the 2022 Internet Crime Report, which is based on internet crimes reported to the IC3. Phishing continues to be the top crime reported, and investment scams were the most financially damaging. Though the IC3 received five percent fewer complaints in 2022 the total loss ballooned from $6.9 billion in 2021 to over $10.2 billion in 2022. By the Numbers – 2022 FBI Internet Crime Report Internet Crime Overview BEC: There were 21,832 BEC complaints with a loss of over $2.7 billion. BEC exploits target organizations and individuals in an effort to redirect funds to fraudulent accounts. Investment Scams: For the first time since the FBI has issued the Internet Crime Report, investment fraud was the costliest crime with losses coming in at $3.31 billion; in 2021, losses were $1.45 billion. There was an unprecedented increase in crypto-investment extortion
Though there can be a wide variation of size, complexity and stage of a DMARC project, they all share a common challenge of understanding when it’s appropriate to advance your policy. This guide will touch on key considerations, milestone validation tips, and DNS syntax guidelines necessary to help you confidently progress your domains to a stringent DMARC policy of p=reject. DMARC Policies First, a brief overview of DMARC policies; the sequence in which they are traditionally applied; and how they vary in protections against phishing, spoofing and unauthorized use of your domains: The three policy modes are none, quarantine and reject. These policies are most traditionally applied in the sequence listed above. Under certain circumstances, it may be appropriate to apply a more stringent policy at the beginning if, for example, you are applying DMARC to a parked or inactive domain. Organizations that receive your email, will look at the
“SPF Flattening” was invented by dmarcian as part of the initial release of the SPF Surveyor. For many years the functionality was flagged as “experimental.” Today, we’re concluding the experiment and sharing what we’ve learned. Sender Policy Framework (SPF) Background Email operators use SPF to identify themselves and their infrastructure when sending email across the internet. SPF was originally created by email operators around 2000 in response to Joe Job Attacks. At that time, spammers were making victims out of legitimate email operators by pretending to be them while sending spam. Legitimate operators were blamed for sending spam simply because there was no easy way to identify email operators and their infrastructure. Email operators publish SPF records to describe their email infrastructure. These records are specially formatted strings of text that live in the DNS. When receiving email, an email server looks at the domain of the sending operator’s email
On January 1, 2022, dmarcian launched its official MSP program. While we’ve worked with MSPs for many years, the formalized program was born out of a desire to reach more domain owners in an effort to spread DMARC even further into the ecosystem. More specifically, we recognized that SMBs, owning a healthy percentage of commercial domains, were quickly pushed through a digital transformation due to COVID-19 and were looking to MSPs for assistance through those changes. Now that we have come a full year since the program launch, we are taking this opportunity to reflect on what we’ve learned from MSPs and envision where we will take the program in the future. Our MSP program philosophy aligns with dmarcian’s mission of increasing accessibility to DMARC technology to make email and the internet safer. MSP Program Manager Joe Garner says, “We realized there was a huge group of email users that