Ecosystem News
Here’s some long-time-coming news from Microsoft, one of the world’s largest mailbox providers: they have started rolling out changes to honor DMARC policies as published in a domain’s DNS. Microsoft will now be treating the p=reject policy as intended; email failing DMARC authentication will not be delivered. Microsoft had been treating the DMARC policies of p=quarantine and p=reject the same way; email failing DMARC with a p=reject policy was delivered to the spam folder. Microsoft said they had operated this way “because some legitimate email may fail DMARC. For example, a message might fail DMARC if it’s sent to a mailing list that then relays the message to all list participants. If Microsoft 365 rejected these messages, people could lose legitimate email and have no way to retrieve it. Instead, these messages will still fail DMARC but they’ll be marked as spam and not rejected.” Microsoft signaled the change to
Updated July 17, 2023 to reflect new statistics from the SBA. dmarcian’s MSP Program Manager, Joe Garner, offers his thoughts on MSPs and their ever increasing role in protecting small and medium businesses from digital attacks. COVID shows the importance of MSPs as a vital touchpoint with the cybersecurity world There was a time in the not-too-distant past when most small businesses didn’t need any IT expertise beyond setting up printers and configuring accounting software, as most of their business was in real-time and in person. As COVID transformed the world, these businesses began adopting digital strategies for the first time to handle operations like digital commerce and remote workforces, and widespread digital transformation began. According to Salesforce’s 2021 “Small and Business Trends” report, 71% of growing small- and medium- sized businesses (SMBs) survived the pandemic by going digital, and 66% say their businesses could not have survived the pandemic
Investment Scams Costliest The FBI’s Internet Crime Complaint Center (IC3) has released the 2022 Internet Crime Report, which is based on internet crimes reported to the IC3. Phishing continues to be the top crime reported, and investment scams were the most financially damaging. Though the IC3 received five percent fewer complaints in 2022 the total loss ballooned from $6.9 billion in 2021 to over $10.2 billion in 2022. By the Numbers – 2022 FBI Internet Crime Report Internet Crime Overview BEC: There were 21,832 BEC complaints with a loss of over $2.7 billion. BEC exploits target organizations and individuals in an effort to redirect funds to fraudulent accounts. Investment Scams: For the first time since the FBI has issued the Internet Crime Report, investment fraud was the costliest crime with losses coming in at $3.31 billion; in 2021, losses were $1.45 billion. There was an unprecedented increase in crypto-investment extortion
Though there can be a wide variation of size, complexity and stage of a DMARC project, they all share a common challenge of understanding when it’s appropriate to advance your policy. This guide will touch on key considerations, milestone validation tips, and DNS syntax guidelines necessary to help you confidently progress your domains to a stringent DMARC policy of p=reject. DMARC Policies First, a brief overview of DMARC policies; the sequence in which they are traditionally applied; and how they vary in protections against phishing, spoofing and unauthorized use of your domains: The three policy modes are none, quarantine and reject. These policies are most traditionally applied in the sequence listed above. Under certain circumstances, it may be appropriate to apply a more stringent policy at the beginning if, for example, you are applying DMARC to a parked or inactive domain. Organizations that receive your email, will look at the
“SPF Flattening” was invented by dmarcian as part of the initial release of the SPF Surveyor. For many years the functionality was flagged as “experimental.” Today, we’re concluding the experiment and sharing what we’ve learned. Sender Policy Framework (SPF) Background Email operators use SPF to identify themselves and their infrastructure when sending email across the internet. SPF was originally created by email operators around 2000 in response to Joe Job Attacks. At that time, spammers were making victims out of legitimate email operators by pretending to be them while sending spam. Legitimate operators were blamed for sending spam simply because there was no easy way to identify email operators and their infrastructure. Email operators publish SPF records to describe their email infrastructure. These records are specially formatted strings of text that live in the DNS. When receiving email, an email server looks at the domain of the sending operator’s email
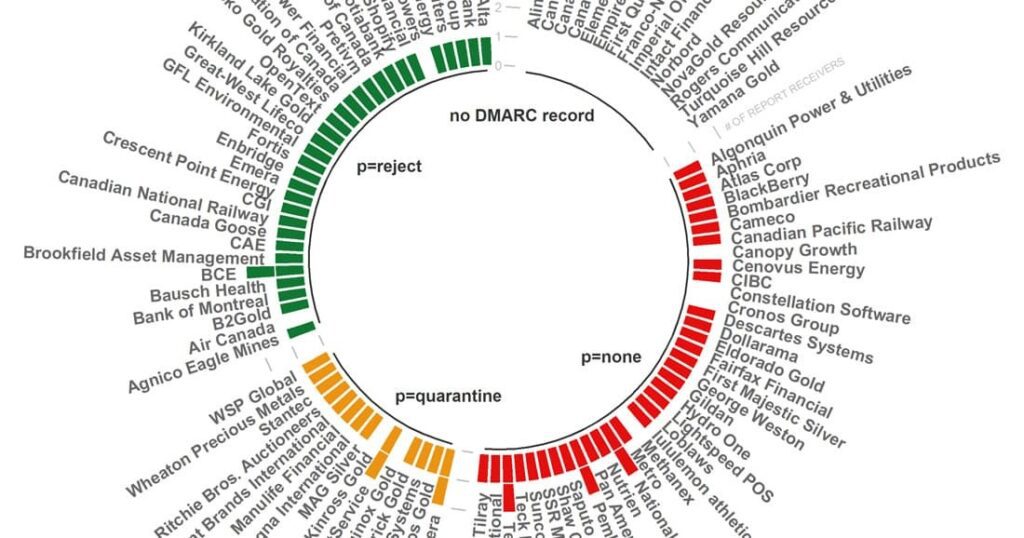
In June 2021 we published research on DMARC adoption among the top 100 companies in Canada. Twenty months later, we evaluated the DMARC adoption rate and are excited to share those rosy results. Here’s the DMARC adoption rate comparison for Canada’s top 100 countries, measured in percentage increase or decrease, from June 2021 to February 2023: 154% increase of DMARC policies set to p=reject 114% increase of DMARC policies set to p=quarantine 18% decrease of DMARC policies set to p=none 57% decrease of companies lacking a DMARC policy Above all, a fifth of the top Canadian companies advanced their DMARC policies to the ultimate goal of a p=reject DMARC policy. With a p=reject policy in place, emails failing DMARC authentication aren’t delivered to the destined inbox. Another fifth took the initial step in securing their domains by establishing DMARC records. People typically begin their road to DMARC compliance by employing
A year ago we surveyed DMARC adoption among the 100 global retailers based on revenue. With the 2022 holiday shopping season ramping up, we’re taking a look to see how retailers are progressing with DMARC adoption. Here’s the comparison, measured in percentage increase or decrease, from last year’s DMARC adoption numbers: 30% increase of DMARC policies set to p=reject 80% increase of DMARC policies set to p=quarantine 10% decrease of DMARC policies set to p=none 16% decrease of companies lacking a DMARC policy The trend illustrates a progression of DMARC compliance in the growth of p=quarantine and p=reject policies from 2021. That’s nothing but good news for retailers and their customers. For the retail, hospitality, and travel community, the holiday season is the most intense time of year for consumers and cybersecurity professionals facing persistent threats. From the beginning of October through the end of December, cyber threats to organizations
The dmarcian team categorizes the sources we see our customers use and include resources that assist in configuring sources to send DMARC-compliant email. Sometimes, however, we are unable to find any publicly available documentation on how to achieve DMARC compliance for a particular source—a service that sends email on behalf of another domain. In these cases, the customer must reach out to the source, or vendor, to request assistance. “Not all third-party providers officially support DMARC, and their first response may be negative,” says Ash Morin, dmarcian’s Director of Deployment. “However, the reality is that they may simply not understand the scope of the request. In our experience, a service provider will often find out that they are in fact capable of supporting DMARC once the requirements are explained clearly to them.” If you find yourself in a situation where you need to contact a source but don’t know what
By default, Microsoft 365 handles inbound emails failing DMARC for domains with a DMARC policy of reject the same way as if they had a policy of quarantine. Read more here about how Microsoft 365 handles inbound email that fails DMARC. Administrators can specify an action to be taken on emails classified as “spoof” through configuring an anti-phishing policy; however, none of these actions include rejecting the email with an error code. After all, a domain owner who has gone through the process of deploying a DMARC policy of reject would want to be alerted of emails being rejected. You may also wish to reject emails failing DMARC where your own domain is being spoofed. This can be achieved through the use of an Exchange mail flow rule. An email that failed DMARC where the domain has a reject policy published will be marked in the Authentication-Results headers by Microsoft
To ensure your Google Calendar invites make it to the intended destination, configure DKIM signing using these steps. The post How to get Google Calendar Invites to Pass DMARC appeared first on dmarcian.