Email Blogs
I’ve seen a bunch of folks panic about some phrasing in Google’s Email sender guidelines. Buried deep in the Message formatting section Google say: Don’t use HTML and CSS to hide content in your messages. Hiding content might cause messages to be marked as spam. Read literally that might cause you to wonder about your use of CSS display:none to switch between different content on desktop and mobile. But that’s not what Google are concerned about – they’re targeting spammers who load up their mail with hidden text (“hashbusters“) in an attempt to make the content of the mail look like one thing to spam filters and a completely different thing to the human recipient. And a variety of similar deceptive behaviour intended to avoid spam filters, or avoid the spam folder or the promotions tab. (This is common behaviour amongst bottom of the barrel spammers. If you see someone
I wrote last year about using “stunt” nameservers for customer subdomain authentication – i.e. dynamically generating all the authentication records needed in DNS for each customer as needed. For example, if you’re an ESP that has customers who can’t or won’t use their own domains and you still need to give them unique subdomains you can generate CNAME records to support white label DKIM authentication: selector ._domainkey. customerid .espcustomer.com CNAME selector .dkim.esp.com or generate white label DMARC with useful rua= reporting: _dmarc. customerid .espcustomer.com TXT “v=DMARC1 p=none rua=rua+ customerid @esp.com” Once you’ve set up these DNS records once they’ll work for all your customers, you just need to put the right domains in your DKIM signature and return path. I shared some demo code to explain the concept last year, but since then we’ve developed a robust, production-ready application to dynamically serve DNS in this way. It’s called
We just got back from Amsterdam a couple of days ago, after attending the Deliverability Summit. It may have been the best email event I’ve been to in several years. Not too big, not too small. Plenty of space and time to meet up with folks. Mostly great sessions, a better average than most conferences. Well organized, at a lovely location, with a safe and welcoming environment. Andrew et al. did a great job putting it together. A better return on time and effort than some of the bigger conferences. Keep an eye out for it next year; maybe we’ll see you there.
When trying to find out why Something Went Wrong during delivery of an email we sometimes want to look at the route by which it was delivered. Did SPF break because of an unexpected forward? Did DKIM break because an intermediate mailserver modified the content of the message? Why did it take nine hours from the mail leaving our ESP to make it to the inbox? Did it really leave our ESP when they say it did? Did Microsoft internal handoffs break something again? Received headers are the breadcrumbs that record the path an email took. Every time a mailserver receives an email it adds a Received header at the top of the mail (so the most recent Received headers come first). And it mustn’t modify any of the existing Received headers. A Received header looks complex, but they have quite a strict structure, and they’re fairly easy to read
Six years ago today I wrote here “Spam isn’t going away“, talking about systemic problems at Google, Cloudflare and Amazon and in India. If I were writing it today I might mention Microsoft, Salesforce and ExactTarget as well as Google, and might stress Amazon less (mostly because all the Amazon spam sites tend to be hidden behind Cloudflare, so you don’t know they’re Amazon sites). And OVH, of course. But the gist of the story hasn’t changed in six years, and the conclusion is as valid today as it was then: There will be increasing volumes of B2B spam being sent for the foreseeable future, and there doesn’t seem to be much we can do to change that. If your career involves filtering inbound spam – consumer, smb or enterprise – it seems your skills will be in demand for a long while yet.
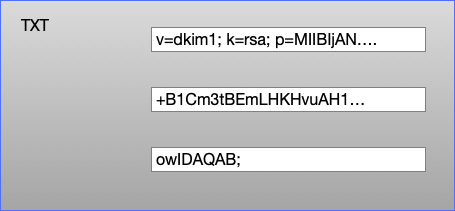
TXT Records DKIM public keys live in DNS TXT records. A DNS TXT record contains strings of text, and each string is limited to be no more than 255 characters long. Recommended practice for DKIM at the moment is to use 2048 bit keys (1024 bit keys aren’t insecure, but they’re looking a bit weak and 2048 is where folks have mostly decided to move to). But a 2048 bit DKIM key is going to be around 400 characters long. So how do we fit that into a TXT record? A TXT record can contain more than one string, so we can split the 400 character public key into two strings, put both of those strings in a single TXT record and the DKIM validator will join those two strings back together and use them to validate the email. A single TXT record containing three strings Editing your DNS Unfortunately
Here’s a bonus Salesforce Marketing Cloud tip for those SFMC users out there in Spam Resource land. Wondering how to configure the Reply Mail Management reply handling functionality? If so, very smart SFMC wizard Donna Redmond has got just what you need: a blog post (and a package manager and video) that explain what you can do with this functionality, and how to configure it. Check it out here.
If you didn’t already know, that screenshot that’s been all over social media, suggesting that Google is telling users that Gmail is to be sunsetted in August 2024, is a hoax. Don’t believe the hype. You can read more on this from the BBC here. An interesting side note: Apparently Elon Musk used this as an opportunity to suggest that a Musk-provided alternative, called X Mail, is coming. There isn’t much more to say about that until/unless something actually happens. Stay tuned.
Yes, I do have various Google alerts set up watching for food-related spam articles. Or SPAM, in this case! Without those alerts, I wouldn’t have stumbled across this deliciously described spam fried rice recipe courtesy of the Recipe Critic. A simple combination of pan-fried spam, fluffy rice, eggs, and veggies, it seems very much like your typical fried rice recipe, but the addition of the diced, salty SPAM luncheon meat kicks things up a notch and this one is going on my “gotta try this” list immediately. Spam Fried Rice Recipe | The Recipe Critic
It’s time to decode another deliverability acronym. Today, we’re going to tackle NDR, which stands for “Non-Delivery Report.” NDR is another way to say “bounce message.” I consider them essentially to be synonyms. In my opinion, the acronym NDR is a bit of a Microsoft-ism, and the more appropriate generic term is probably “bounce message.” What’s a bounce message? Whenever you try to email somebody, but you get a notification email back that tells you that your attempt to mail that someone was unsuccessful. That response, notifying you of the delivery failure is an NDR or bounce message. When you use an email service provider, CRM or newsletter tool to send email messages, these tools typically receive and process any bounces for you automatically. It’s not always necessary to generate a whole NDR email message when a message doesn’t go through — much of the time, when a newlsetter tool