DMARC benefits
Our EU Director Dermot Harnett and Deployment Representative Matia Boldrini joined Dublin City University’s Information Systems Services (ISS) Team on April 9, 2024, to discuss the lessons learned and challenges overcome during DCU’s journey to DMARC compliance. The presenters take a straightforward, candid look at the DCU DMARC project, stressing the importance of building relationships and support among university departments and the coworkers that lead them. As you’ll learn in the presentation, DCU ISS was motivated by the NCSC’s email security guidance, and began their DMARC discovery phase, including advocacy among the university leadership and an initial trial with dmarcian. The ISS team shares their challenges for prioritizing this project and how they informed university stakeholders through meetings and internal communications. With the visibility gained through DMARC, they also talk about how they discovered redundant IT resources and were able to gain efficiency. If you weren’t able to join us
Ash Morin, our Director of Deployment, joined Mailgun’s Email’s Not Dead podcast crew to discuss Google and Yahoo’s DMARC sender requirements, which they began enforcing on February 1, 2024. Ash was a guest on Email’s Not Dead S2 E7—Spoofing, Phishing and for the Love of DMARC and on S3 E5—Implementing DMARC. In S5 E4, faithful hosts Jonathan Torres and Eric Trinidad asked Ash to join them and provide an overview of what he’s seen and what he predicts with the new email authentication standards update from Yahoo and Google. “Immediately after the announcement we started getting a lot of questions coming in. Not only questions from our existing customer base, but also in ecosystems,” Ash said. “There’s been a lot of ‘what does that mean?’ And almost immediately following, they were asking, ‘does that change anything about the standards? If not, what’s my current state? Am I actually good?’ Even
UPDATES: December 26, 2023: The Department of Defense published for comment a proposed rule for the Cybersecurity Maturity Model Certification (CMMC) 2.0 program. December 7, 2022: DMARC and other specs dropped from CMMC 1.0 have been sent to NIST to be included in future revisions of NIST SP 800-171, which CMMC is based upon. For more recent updates, you can visit the Department of Defense Chief Information Officer webpage. The following was published September 20, 2021. The Cybersecurity Maturity Model Certification (CMMC) is a cybersecurity framework being developed by the Department of Defense (DoD) to protect defense contractors from cyber threats. CMMC measures cybersecurity maturity with five levels consisting of security controls, practices and continual improvement to stop the theft of intellectual property, proprietary information and credentials that threaten economic and national security. When an organization sets out to achieve a particular CMMC level, it must also meet the preceding
The Cybersecurity and Infrastructure Security Agency (CISA), National Security Agency (NSA), Federal Bureau of Investigation (FBI), and Multi-State Information Sharing and Analysis Center (MS-ISAC) have released Phishing Guidance—Stopping the Attack Cycle at Phase One to provide guidance in the ever-waging battle against phishing exploits. The guidance is relevant to all organizations, though it may pose challenges for those with limited resources. To address this, the guide incorporates a section with customized suggestions tailored for small- and medium-sized businesses that may lack the resources for a dedicated IT staff to consistently combat phishing threats. For software manufacturers, the emphasis is on adopting secure-by-design and default strategies. The guidance encourages software companies to create and deliver software that is resistant to common phishing threats, ultimately enhancing the cybersecurity resilience of their customers. In the phishing mitigation guidance for all organizations, CISA, NSA, FBI, and MS-ISAC recommend organizations implement DMARC and other controls
Ransomware, Act I The first documented ransomware attack was delivered by the postal service in 1989 when 20,000 floppy discs loaded with malware were sent to AIDS researchers across the globe with the promise of advancing research. When loaded in computers, the discs installed malware and displayed a ransomware message demanding payment to restore data and systems. The attacker, an AIDS researcher himself, took advantage of other researchers to capitalize on the urgency and uncertainty of the AIDS epidemic. Cybercriminals continue to employ similar scare tactics today, using coercion, matters of necessity and social engineering to dupe unsuspecting people. Instead of using snail mail, cybercriminals use unprotected domains to send spoofed emails for deploying ransomware. What is Ransomware? The Cybersecurity and Infrastructure Security Agency (CISA) defines ransomware as a type of malware “cyber actors use to deny access to systems or data. The malicious cyber actor holds systems or data
“Technologies recommended in support of core Simple Mail Transfer Protocol (SMTP) and the Domain Name System (DNS) include mechanisms for authenticating a sending domain: Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM) and Domain based Message Authentication, Reporting and Conformance (DMARC).” The post National Institute of Standards and Technology (NIST) Provides DMARC Guidance appeared first on dmarcian.
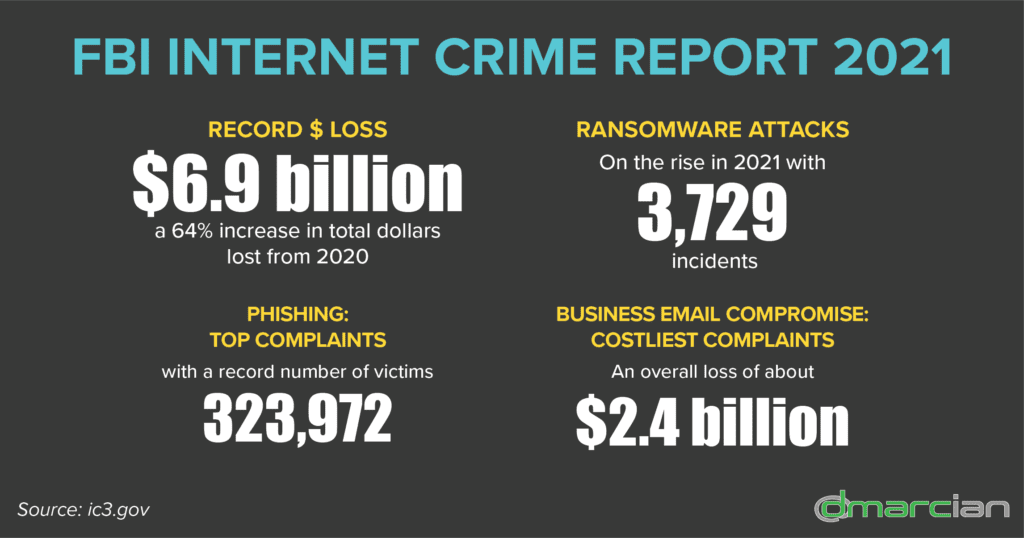
Because of the accessibility of email, we’ve seen increased abuse that has become more sophisticated over the years. Business email compromise (BEC) attacks cost organizations an estimated $2.4 billion in losses in 2021 in the US alone. The post What is Business Email Compromise (BEC)? appeared first on dmarcian.
Our DMARC deployment experts often hear from customers about email from mailing lists not being delivered. Have you run up against this challenge in your DMARC project? The post Mailing Lists and DMARC appeared first on dmarcian.
To provide a second step beyond your password in proving and securing your online identity, Multifactor Authentication steps in as a double-check in the authentication process. The post Enhance Your Security Stance with Multifactor Authentication appeared first on dmarcian.
In 2021, IC3 continued to receive a record number of complaints from the American public: 847,376 reported complaints, which was a 7% increase from 2020, with potential losses exceeding $6.9 billion. The post 2021 FBI Internet Crime Report appeared first on dmarcian.